The End of Disconnected Silos!
Building a Targeted Harm Recognition and Response Stack (THRRS)
Most organizations understand “stacks.”
You have a cybersecurity stack because no single tool can see everything. You have a sales stack because revenue depends on clean handoffs and shared visibility. You have a training stack because development doesn’t happen in one workshop.
Stacks exist for one reason: disconnected data creates blind spots—and blind spots create unforced errors.
Now the hard question: when it comes to targeted violence, do you have a stack? Or do you have a handful of tools spread across HR, Security, Legal, Facilities, and IT—each doing its own job, but rarely working together?
Why siloed threat assessment fails
After 30 years in physical security and enterprise risk management, I’ve watched the same pattern repeat:
* HR owns a reporting channel and case notes.
* Security owns cameras, access control, and incident logs.
* Facilities owns keys, badges, and vendor access.
* A Threat Assessment Team gets pulled in when things feel “serious.”
Then a behavioral crisis hits—and everyone expects one tired team member to manually connect the dots in real time. That’s not a prevention strategy, it’s hope dressed up as process.
The THRRS approach
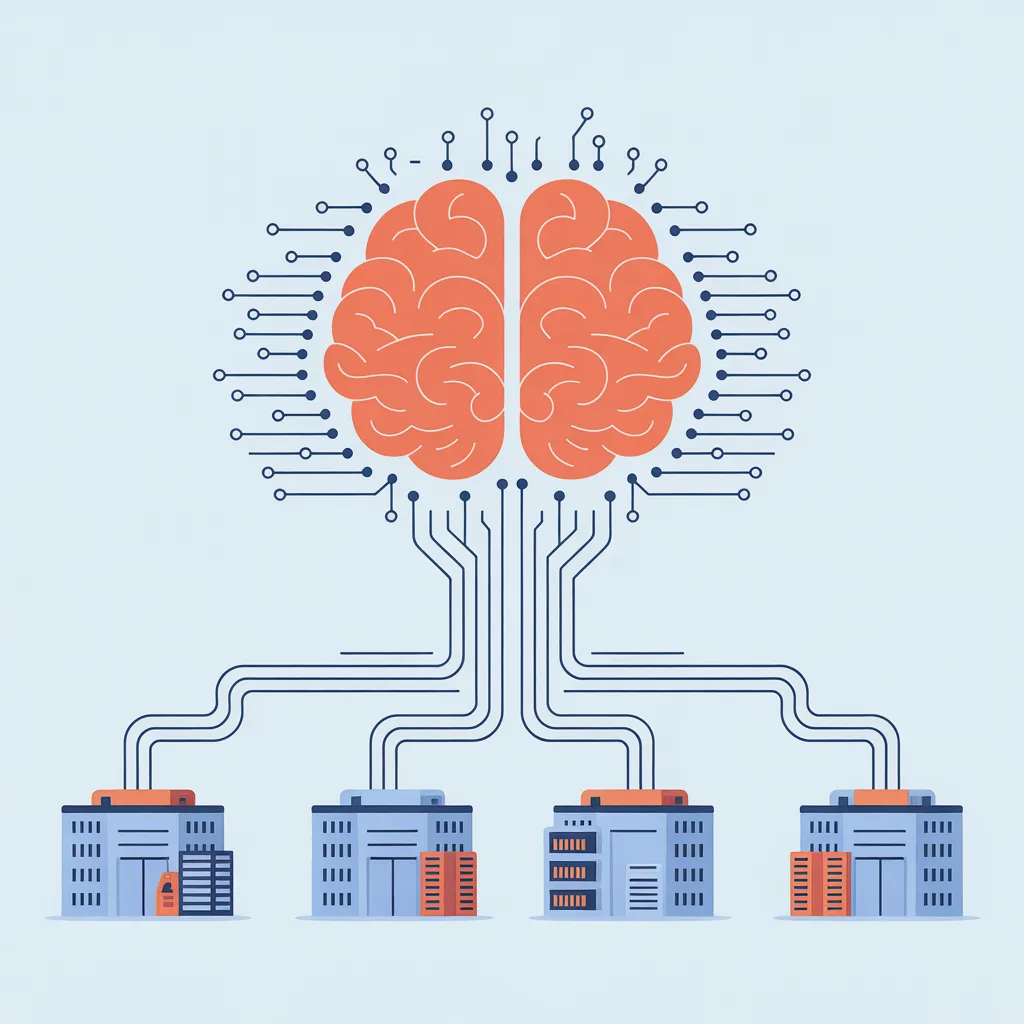
This is exactly why I built Threatalytics AI—not as another standalone tool, but as the “brain” inside a cohesive architecture we call the Targeted Harm Recognition and Response Stack (THRRS).
THRRS is four operational layers that connect your existing assets into one defensible workflow:
Layer 1: Sensor Network (Signals In) Your structured reporting pathways, HR records, internal case data, and other authorized inputs. This layer collects signals—but by itself, it’s just storage.
Layer 2: Recognition Engine (Threatalytics AI) — The Brain Threatalytics AI is a multilingual cognitive Assistive Intelligence overlay for professional threat assessment teams. Designed to help triage cases while adding deep insights for professional guidance. Not predictive or meant to diagnose. This is the logic layer that cross-examines incoming signals using our VALT framework:
* V — Velocity: How fast is escalation happening?
* A — Alternatives: Is the subject showing “loss of options” or desperation?
* L — Leakage: Are there breadcrumbs—statements, messages, third-party disclosures?
* T — Thresholds: Are they crossing tripwires like probing, access attempts, or acquisition behaviors?
This is decision support, not a verdict. Human review is a must and non-negotiable.
Layer 3: Human Governance (Your TAT / MDT) Your multidisciplinary Threat Assessment Team—HR, Legal, Security, Behavioral Health, Operations. With a shared roadmap from Layer 2, the team stops debating opinions and starts aligning on documented, legally defensible decisions.
Layer 4: Response & Resolution (Action Out) This is where your organization executes: EAP handoffs, administrative controls, safety planning, workplace adjustments, terminations done safely, and—when appropriate—law enforcement coordination.
Closing the Capacity Gap
If you have sensors (Layer 1) and response resources (Layer 4), but no recognition engine connecting them (Layer 2), you don’t have an intervention strategy.
You have blind spots waiting to be exposed.
With Threatalytics AI ,we help you connect the stack—turning scattered data into recognition, and recognition into coordinated action.
Ready to see what THRRS looks like in your environment? Book a demo.